Secure Data Management: Protecting Your Secret Information
In this post, we will certainly go over the value of protected data administration and provide you with best techniques to secure your beneficial information. You'll discover regarding usual dangers to your info and just how to apply reliable information file encryption.
The Value of Secure Data Management
The significance of secure information administration can't be overemphasized in today's electronic age. As a private, you rely upon technology for numerous elements of your life, whether it's online financial, social media sites, or keeping personal details. With the enhancing prevalence of cyber dangers, it is critical to prioritize the security of your information.

When you manage your data securely, you ensure that just authorized people have accessibility to your secret information. This secures you from identity theft, monetary fraud, and also various other harmful activities. By executing strong passwords, security, and also routine backups, you dramatically lower the danger of your data falling under the wrong hands
Secure information administration also profits companies and companies. As an organization owner, you have a responsibility to secure your customers' delicate data, such as bank card details or personal information. Failure to do so can cause reputational damage, legal repercussions, and monetary losses. By focusing on safe data monitoring practices, you show your commitment to securing your clients' privacy as well as structure count on within your neighborhood.
Usual Dangers to Secret Information
Understand typical dangers that can jeopardize your confidential information. As innovation developments, so do the techniques of cybercriminals. It is critical to stay notified concerning the different threats that might potentially put your sensitive info in danger. One usual hazard is phishing attacks, where opponents attempt to deceive you into revealing your individual info with deceptive e-mails or internet sites. These e-mails typically appear legitimate, yet they are developed to steal your login credentials or economic information. Another risk to be careful of is malware, which can be unknowingly downloaded and install onto your gadget. This malicious software can gain unapproved accessibility to your confidential information or perhaps take control of your device. Furthermore, unconfident Wi-Fi networks can pose a substantial danger. Cyberpunks can intercept your information when you connect to unsecured networks, possibly exposing your financial and also personal info. Last but not least, social engineering strikes include manipulating individuals into divulging private details. These assaults can be accomplished with phone telephone calls, emails, and even personally. By being aware of these typical hazards, you can take proactive actions to secure your personal data as well as guarantee your online safety.

Best Practices for Information File Encryption
When it comes to securing your confidential information, information security is important. Security transforms your data right into a secret code, making it unreadable to unauthorized individuals.
Prevent making use of usual expressions or conveniently guessable details, such as your name or birthdate. This means, even if one password check is jeopardized, your other accounts stay protected.
Keep in mind to consistently update your passwords to maintain a high level of safety and security. Set pointers to change your passwords every couple of months or whenever there is an information violation. By doing so, you minimize the danger of somebody acquiring unauthorized accessibility to your private information.
Implementing Access Controls and Customer Consents
Make sure that you on a regular basis readjust and also evaluate accessibility controls and also user consents to maintain the security of your delicate information. By applying efficient gain access to controls and user approvals, you can significantly lower the threat of unauthorized access to your confidential details.
Begin by routinely evaluating the access controls in position. This includes assessing that has access to what data as well as guaranteeing that it aligns with their functions as well as responsibilities within the company. As workers leave the business or sign up with, it is crucial to promptly update their access benefits to stop any kind of potential breaches.
Along with assessing gain access to controls, it is vital to readjust individual consents as required. Customer approvals determine what activities an individual can do on the data they have access to. By approving the appropriate degree of consents per customer, you can limit their capabilities as well as lessen the threat of data misuse or unexpected deletion.
Consistently assessing and also changing accessibility controls and individual approvals is an ongoing procedure - Cyber Security. As your organization progresses as well as expands, it is crucial to stay on par with changes as well as make certain that your data remains safe and secure. By doing so, you can protect your delicate details from unauthorized accessibility and also preserve the stability and also privacy of your information
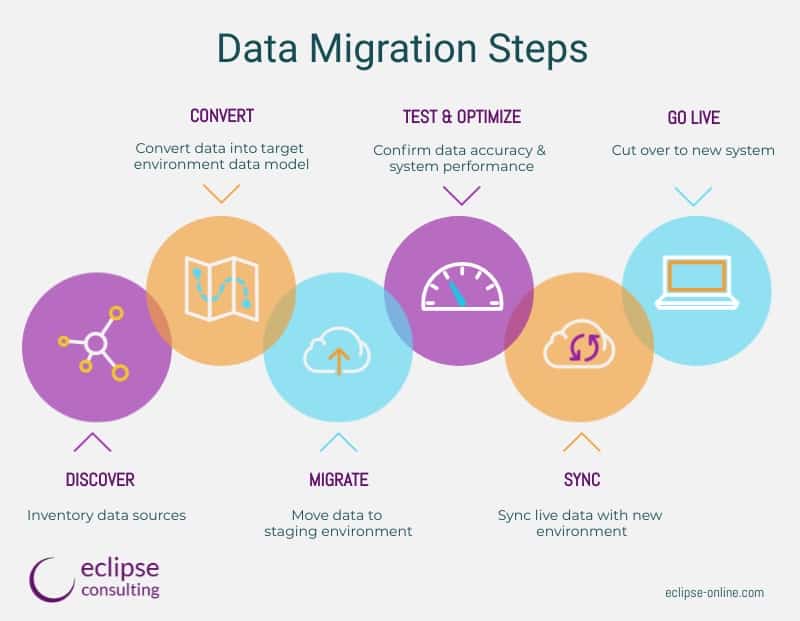
Data Back-up and Catastrophe Recuperation Procedures
Consistently supporting your data is important for catastrophe recovery in case of unforeseen events. It is vital to have a back-up strategy in area to shield your beneficial info as well as guarantee business continuity. By routinely backing up your information, you can lessen the impact of information loss due to hardware failings, all-natural disasters, or cyberattacks.
Having a dependable back-up system enables you to restore your information swiftly and successfully, lowering downtime and also stopping potential economic losses. Whether you select to back up your information on external hard drives, cloud storage space, or a combination of both, it is essential to arrange regular backups to guarantee that your most recent info is protected.
Along with regular back-ups, it is similarly crucial to test your back-up systems and processes regularly. When needed, this makes certain that your backups are working effectively and that you can efficiently restore your information. By examining your backup systems, you can recognize any kind of possible issues or spaces in your calamity recuperation plan as well as address them proactively.
Conclusion
Finally, handling and securing your private information is important in today's electronic landscape. Managed IT Services. By executing safe and secure information administration look at more info practices such as encryption, gain access to controls, and also data backup measures, you can secure your important information from typical hazards. Bear in mind to regularly update your safety and security procedures to remain one step ahead of prospective breaches. By prioritizing the safety and security of your private details, you can ensure the count on and confidence of your clients and stakeholders. So, don't wait any longer, take action now to safeguard your information!
In this article, we will certainly review the importance of safe and secure information administration and give you with ideal techniques to secure your navigate to this website important information. When you handle your data firmly, you make sure that only authorized people have access to your confidential info. When it comes to safeguarding your private information, information encryption is crucial. By consistently backing up your information, you can lessen the impact of information loss due to hardware failings, all-natural catastrophes, or cyberattacks.
By executing secure information management methods such as encryption, gain access to controls, and information backup steps, you can guard your important information from common dangers.